CyberSecurity
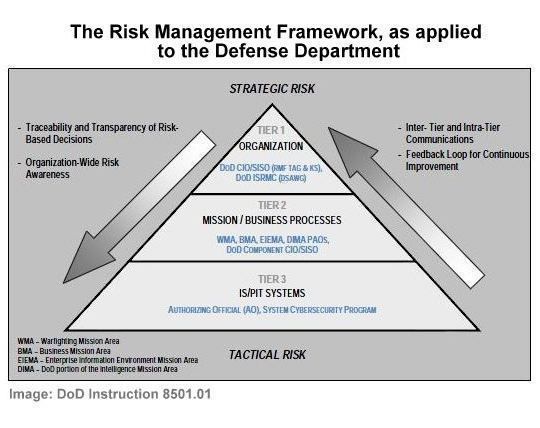
Cybersecurity threats individuals and organizations are both challenging and complex. People have the daunting responsibility to minimize cybersecurity vulnerabilities in their systems against current and future cybersecurity threats. To effectively address cybersecurity threats you need a combination of the right policies, processes, people and tools. And - cybersecurity is dynamic by nature, requiring proactive engagement and expertise to minimize risk throughout your systems and programs. Effective cybersecurity can only be achieved through a holistic approach that takes into account more than just information assurance compliance. Such a holistic approach must include areas of known cybersecurity risk and potential future cybersecurity risk and provide an effective framework for developing, planning and implementing an efficient and effective cybersecurity strategy.